The Lost Paradise
By: Samson Kamson
Read full @ shorter.me/AqFtm

Read more / Original news source: https://nitter.net/epaomanipur/status/2065069135042900000#m
The Lost Paradise
By: Samson Kamson
Read full @ shorter.me/AqFtm
The Lost Paradise
By: Samson Kamson
Read full @ shorter.me/AqFtm

Read more / Original news source: https://nitter.net/epaomanipur/status/2065069135042900000#m
RHYTHM & IMPRESSION : A Solo Art Exhibition by Dr Gurumayum Krishnadas Sharma on 7th June, 2026, at Imphal Art Gallery, Kwakeithel Leimakhujam Leikai, Airport Road, Imphal West.
See full gallery @ shorter.me/eT3QB
Picture Credit :: David M Mayum
…
RHYTHM & IMPRESSION : A Solo Art Exhibition by Dr Gurumayum Krishnadas Sharma on 7th June, 2026, at Imphal Art Gallery, Kwakeithel Leimakhujam Leikai, Airport Road, Imphal West.
See full gallery @ shorter.me/eT3QB
Picture Credit :: David M Mayum




Read more / Original news source: https://nitter.net/epaomanipur/status/2065068750525886482#m
Violence in Manipur
NEWS TIMELINE
11 June 2026
Barely 24 hours after 14 Kuki hostages released safe and sound…Six abducted Naga men found dead
PREPAK flays CRPF DG’s statement
UNC condemns, imposes 24 hr bandh
Read all related news @ bit.ly/3RzPwau
Violence in Manipur
NEWS TIMELINE
11 June 2026
Barely 24 hours after 14 Kuki hostages released safe and sound…Six abducted Naga men found dead
PREPAK flays CRPF DG’s statement
UNC condemns, imposes 24 hr bandh
Read all related news @ bit.ly/3RzPwau
Read more / Original news source: https://nitter.net/epaomanipur/status/2065067156283564046#m
Manipur’s conflict widens as Kuki-Naga tensions resurface
By: Yambem Laba
Read full @ shorter.me/ZGxJZ
Manipur’s conflict widens as Kuki-Naga tensions resurface
By: Yambem Laba
Read full @ shorter.me/ZGxJZ

Read more / Original news source: https://nitter.net/epaomanipur/status/2065067085387231237#m
Financial Assistance to Victims of 13 May Attack on TBAI Leaders
– 10 June 2026 :: Melbourne Thadou Baptist Church (MTBC) –
Read full @ shorter.me/ayaQo
Financial Assistance to Victims of 13 May Attack on TBAI Leaders
– 10 June 2026 :: Melbourne Thadou Baptist Church (MTBC) –
Read full @ shorter.me/ayaQo

Read more / Original news source: https://nitter.net/epaomanipur/status/2065066304567226848#m
Final Audition for Apatani’s Next Top Model 2026
– Naharlagun, 8 June 2026 :: Fashion & Design Council of Arunachal Pradesh (F&DCAP) –
Read full @ shorter.me/Js7Y4
Final Audition for Apatani’s Next Top Model 2026
– Naharlagun, 8 June 2026 :: Fashion & Design Council of Arunachal Pradesh (F&DCAP) –
Read full @ shorter.me/Js7Y4

Read more / Original news source: https://nitter.net/epaomanipur/status/2065065884142756001#m
“Tharoi Yonbigi Macha” a play presented by Samadon Artist Association at 52nd All Manipur Shumang Leela Festival on 9th May 2026 at Iboyaima Shumang Leela Shanglen
Picture Courtesy :: Khaba Kh
See Archives News Photo @ bit.ly/4aA5AAR
“Tharoi Yonbigi Macha” a play presented by Samadon Artist Association at 52nd All Manipur Shumang Leela Festival on 9th May 2026 at Iboyaima Shumang Leela Shanglen
Picture Courtesy :: Khaba Kh
See Archives News Photo @ bit.ly/4aA5AAR

Read more / Original news source: https://nitter.net/epaomanipur/status/2065065605900964203#m
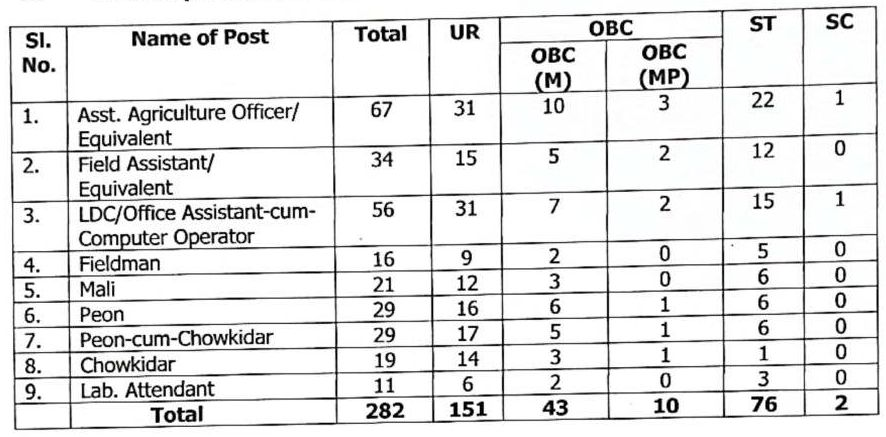
282 Contractual Posts at Department of Horticulture, Manipur
Date: 10th June, 2026 :: Department of Horticulture & Soil Conservation
Read full @ shorter.me/9fYYA
282 Contractual Posts at Department of Horticulture, Manipur
Date: 10th June, 2026 :: Department of Horticulture & Soil Conservation
Read full @ shorter.me/9fYYA
Read more / Original news source: https://nitter.net/epaomanipur/status/2065065293421134080#m
Unauthorized operation of drones in vicinity of Imphal International Airport prohibited
– Date: 10th June, 2026 : Deputy Commissioner, Imphal West –
Read full @ shorter.me/YUA81
Unauthorized operation of drones in vicinity of Imphal International Airport prohibited
– Date: 10th June, 2026 : Deputy Commissioner, Imphal West –
Read full @ shorter.me/YUA81
Read more / Original news source: https://nitter.net/epaomanipur/status/2065065064978338224#m
Taking the art of lying to a new high : Found in bones and rotting flesh
– The Sangai Express Editorial :: June 11 2026 –
Read full @ shorter.me/aMKdP
Taking the art of lying to a new high : Found in bones and rotting flesh
– The Sangai Express Editorial :: June 11 2026 –
Read full @ shorter.me/aMKdP
Read more / Original news source: https://nitter.net/epaomanipur/status/2065064878688403798#m
LISTEN: AIR Manipuri 7:30 AM for 11 June 2026
Listen @ bit.ly/2TLdFxC
Tune into AIR Sangai Radio Channel – 24/7 LIVE Stream @ e-paolive.net/airimphal/
#AIRNews #ManipuriNews #AllIndiaRadioImphal #Manipur #Imphal
LISTEN: AIR Manipuri 7:30 AM for 11 June 2026
Listen @ bit.ly/2TLdFxC
Tune into AIR Sangai Radio Channel – 24/7 LIVE Stream @ e-paolive.net/airimphal/
#AIRNews #ManipuriNews #AllIndiaRadioImphal #Manipur #Imphal

Read more / Original news source: https://nitter.net/epaomanipur/status/2065064786505961655#m
News in Meitei Mayek
Read the news @ shorter.me/UOElH
News in Meitei Mayek
Read the news @ shorter.me/UOElH
Read more / Original news source: https://nitter.net/epaomanipur/status/2065064537330692183#m
Reported by Bhadra Gogoi Dimapur: Nagaland Chief Minister Neiphiu Rio on Thursday condemned the killing of six Naga men in Manipur and urged the Centre and the Manipur government to take urgent steps to ensure that those responsible are brought to ju…


Reported by Bhadra Gogoi Dimapur: Nagaland Chief Minister Neiphiu Rio on Thursday condemned the killing of six Naga men in Manipur and urged the Centre and the Manipur government to take urgent steps to ensure that those responsible are brought to justice. In a social media post, Rio described the killings as “tragic, inhuman and […]
The post Nagaland CM urges Centre, Manipur government to ensure justice for six slain Nagas appeared first on NorthEast Now.
Read more / Original news source: https://nenow.in/north-east-news/nagaland/nagaland-cm-urges-centre-manipur-government-to-ensure-justice-for-six-slain-nagas.html
Manipur: Day After Six Naga Men’s Bodies Discovered, Two Kuki Men Reported Dead TheWire.in
Reported by Bhadra Gogoi Dimapur: The NSCN (IM) has demanded that the Government of India immediately outlaw Kuki militant groups and their affiliated village volunteers, and formally designate them as terrorist organisations following the alleged ki…


Reported by Bhadra Gogoi Dimapur: The NSCN (IM) has demanded that the Government of India immediately outlaw Kuki militant groups and their affiliated village volunteers, and formally designate them as terrorist organisations following the alleged killing of six Naga captives. In a statement, the NSCN/GPRN strongly condemned what it described as the “barbaric killing” and […]
The post NSCN (IM) demands terror tag for Kuki militant groups after killing of six Naga hostages appeared first on NorthEast Now.
Read more / Original news source: https://nenow.in/north-east-news/nagaland/nscn-im-demands-terror-tag-for-kuki-militant-groups-after-killing-of-six-naga-hostages.html
By NE NOW NEWS Imphal: Kuki Inpi Manipur (KIM) on Thursday condemned the killing of two church workers in Kamjong district’s Kultuh village and demanded an independent judicial inquiry into the incident. In a statement, the apex Kuki body alleg…


By NE NOW NEWS Imphal: Kuki Inpi Manipur (KIM) on Thursday condemned the killing of two church workers in Kamjong district’s Kultuh village and demanded an independent judicial inquiry into the incident. In a statement, the apex Kuki body alleged that the killings took place during a pre-dawn raid on the village by armed assailants […]
The post Manipur: KIM seeks probe into alleged involvement of Myanmar-based armed groups in Kamjong killings appeared first on NorthEast Now.
Read more / Original news source: https://nenow.in/north-east-news/manipur/manipur-kim-seeks-probe-into-alleged-involvement-of-myanmar-based-armed-groups-in-kamjong-killings.html
Manipur Violence: 8 Detained After Bodies of 6 Abducted Naga Men Recovered Daily Pioneer
Manipur Violence: 8 Detained After Bodies of 6 Abducted Naga Men Recovered Daily Pioneer
Read more / Original news source: https://news.google.com/rss/articles/CBMingFBVV95cUxNSHZkdmFzS19sQ3ZFVjFNNEFvTWlGRGVWbGZseTVzcXNJUmVZZzR2YkNvU2ZvQ19vcnAwVU94aXlPOVM4bVR5eXRKTU0tTXBRTnNaZVY3VV9UZlo1bGJzbXF5Y21GYmpNcERzNzBianBtbFhSQlF1V05iQ3YtcUtqbDlaa1dKajIwRUprc1VaX0VTNUFQN2cxTE1WMlhkQQ?oc=5
By NE NOW NEWS Guwahati: Eastern Kuki Chiefs’ Association (EKCA) has strongly condemned Thursday’s early morning attack in Kultuh village in Manipur, in which two civilians were killed and seven houses, including a church were set ablaze. The attack …


By NE NOW NEWS Guwahati: Eastern Kuki Chiefs’ Association (EKCA) has strongly condemned Thursday’s early morning attack in Kultuh village in Manipur, in which two civilians were killed and seven houses, including a church were set ablaze. The attack reportedly took place around 4:00 am, during which unidentified armed assailants entered the village and torched […]
The post Manipur: EKCA condemns Kultuh attack, 2 dead and homes destroyed appeared first on NorthEast Now.
Read more / Original news source: https://nenow.in/north-east-news/manipur-ekca-condemns-kultuh-attack-2-dead-and-homes-destroyed.html
Two killed in attacks by armed men in India’s restive Manipur state, police say AOL.com
Two killed in attacks by armed men in India’s restive Manipur state, police say AOL.com
Read more / Original news source: https://news.google.com/rss/articles/CBMifEFVX3lxTE9kSVNydG01OGc5U3JqWG5zQmFJX0EtWDVBX0d2WXluUFR1cEVuc1dSUlJTUENJdl80TTZsZ1pFQnVHc2JRUXMzX1JPckVydkY3MlVwZmpjZTlvZnduYkhqVGt3by1rWHpyQVdVLTNGSXZWYmhhRmdibW1mWnU?oc=5
Two killed in attacks by armed men in India’s restive Manipur state, police say Reuters
Two killed in attacks by armed men in India’s restive Manipur state, police say Reuters
Read more / Original news source: https://news.google.com/rss/articles/CBMiswFBVV95cUxQb2pZakVlbUw1bTlLTTR2SGZmQm5rMEtRZE9fY09pZlBMUW0xemU1WTVCZXNZV3dPbk9ieWdENzZqRTVhMHhuRk9BTDNqenY0N1VTclFWVk8yZDJRRVZWZkQzMmUxcXZib2NwZHN2MUpRMHNjR1R0RUd4TUcwMDJZVG1pMmx5Q3BuT3FvcHB2ZHpkUDktRmcwZEVJeTE3VXlvc1pMWkFaa1VTd3BWaEhqT1JhWQ?oc=5